Introduction
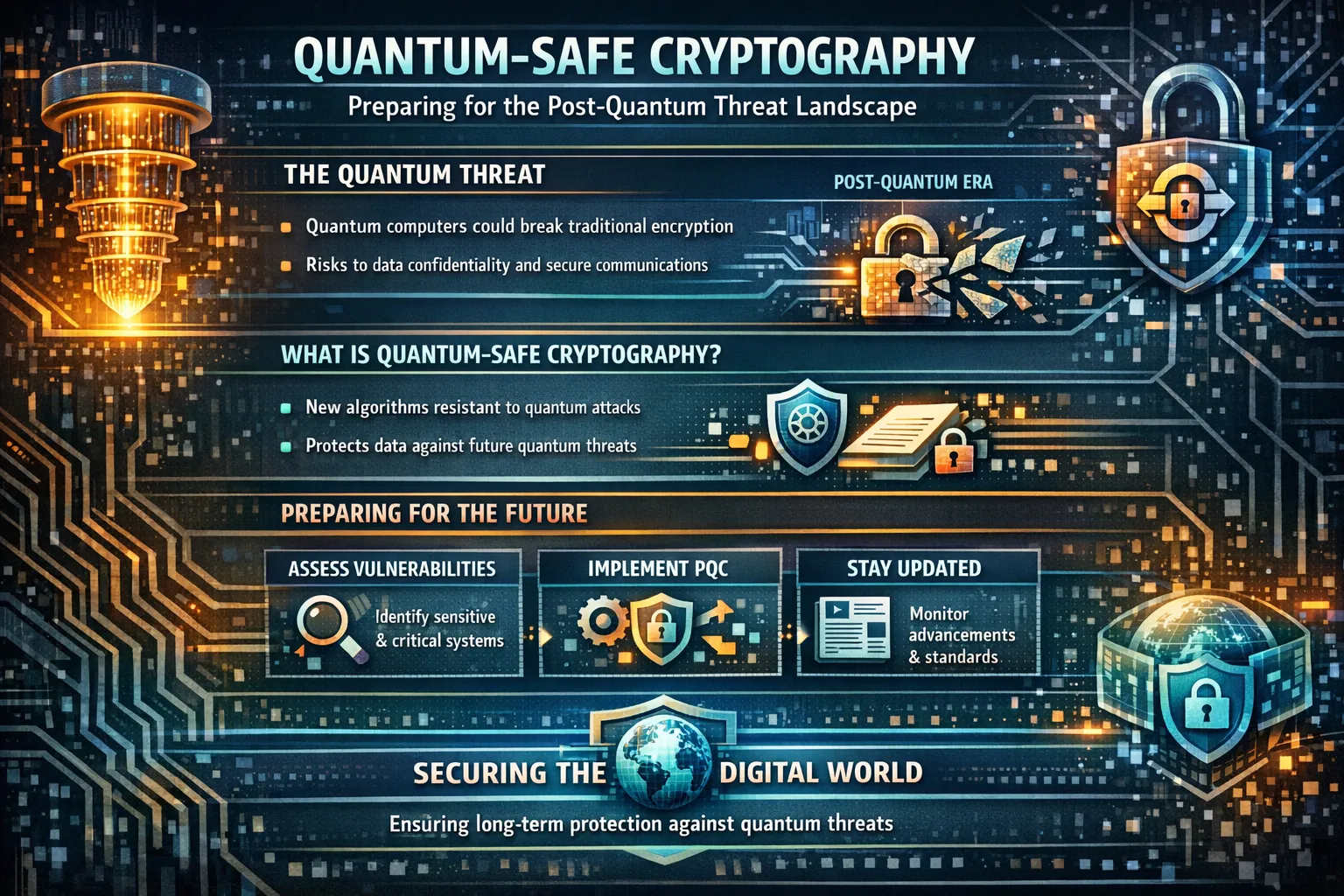
Quantum-safe cryptography (often called post-quantum cryptography or PQC) represents the next generation of cryptographic algorithms designed to resist attacks from both classical and quantum computers. The urgency around quantum-safe cryptography has intensified dramatically. Recent research from Google demonstrates that future quantum computers may break elliptic curve cryptography with far fewer qubits than previously estimated—approximately 500,000 physical qubits could break ECDLP-256 in minutes. This is not a distant theoretical concern. For organizations handling sensitive data with long lifespans—healthcare records, government intelligence, and financial transactions—the transition to quantum-safe cryptography must begin now.
The threat is not speculative. Adversaries are already collecting encrypted data under what security professionals call the “harvest now, decrypt later” (HNDL) attack model. Any encrypted data captured today remains vulnerable to decryption once cryptographically relevant quantum computers (CRQCs) become available. This reality transforms quantum-safe cryptography from a future planning item into a present-day risk management priority.
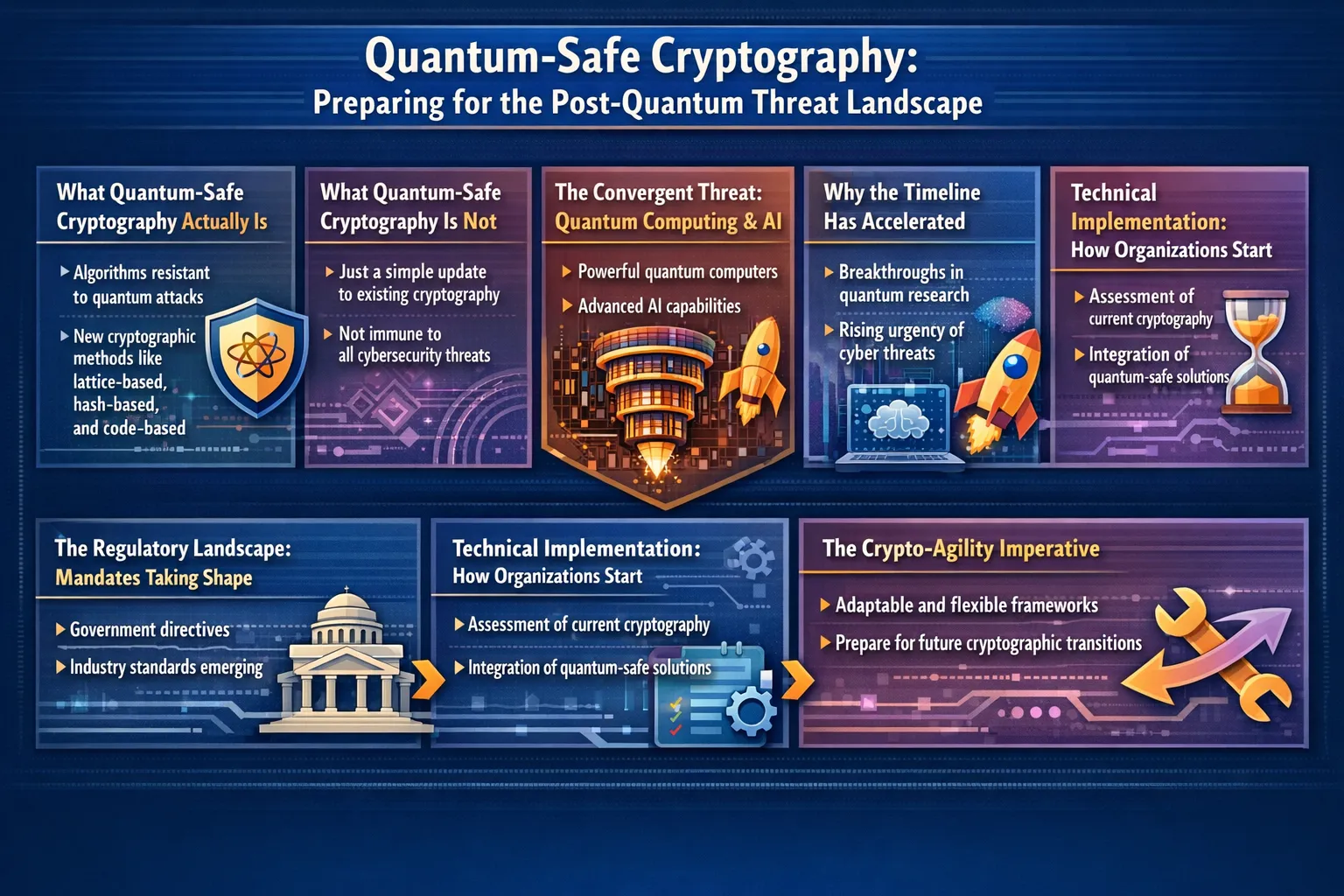
What Quantum-Safe Cryptography Actually Is
Quantum-safe cryptography refers to cryptographic algorithms that remain secure against attacks from both classical computers and quantum computers running Shor‘s algorithm or Grover’s algorithm. This is fundamentally different from quantum cryptography (such as quantum key distribution), which requires specialized hardware. Quantum-safe cryptography runs on existing classical infrastructure—standard servers, laptops, and network equipment.
The National Institute of Standards and Technology (NIST) finalized three quantum-safe cryptographic standards in August 2024:
- FIPS 203 (ML-KEM): A key encapsulation mechanism based on CRYSTALS-Kyber for secure key exchange
- FIPS 204 (ML-DSA): A digital signature scheme based on CRYSTALS-Dilithium
- FIPS 205 (SLH-DSA): A hash-based signature scheme based on SPHINCS+
In March 2025, NIST selected HQC as an additional backup key encapsulation mechanism. These standards provide the foundation for all quantum-safe migration efforts across government and industry.
What Quantum-Safe Cryptography Is Not
Several misconceptions need clearing up. Quantum-safe cryptography is not quantum key distribution (QKD). QKD uses quantum mechanics to detect eavesdropping but requires specialized optical hardware, point-to-point connections, and has distance limitations. Quantum-safe cryptography, by contrast, is purely mathematical and runs anywhere.
Quantum-safe cryptography also does not mean “quantum-proof.” No cryptographic algorithm is provably immune to all future attacks—quantum or otherwise. The term “quantum-safe” acknowledges this limitation. These algorithms resist all known quantum attacks today, but cryptanalysis continues. That is why cryptographic agility matters.
Finally, quantum-safe cryptography does not replace symmetric encryption like AES. AES-256 remains quantum-safe because Grover’s algorithm only reduces its effective security from 256 bits to 128 bits—still practically secure. The real vulnerability lies in public-key cryptography: RSA, ECC, and Diffie-Hellman.
The Convergent Threat: Quantum Computing and AI
Two distinct technological disruptions are challenging current cryptographic systems simultaneously. Quantum computing attacks the mathematical algorithm layer, breaking RSA and ECC in polynomial time. Artificial intelligence attacks the physical implementation layer through side-channel analysis—neural networks extracting keys from power consumption traces, electromagnetic emanations, and timing variations.
This convergence creates unique complexity. Organizations cannot simply swap algorithms and declare them secure. Implementation matters. Side-channel attacks work against quantum-safe algorithms just as they work against classical ones. A lattice-based ML-KEM implementation that leaks timing information remains vulnerable regardless of its mathematical robustness.
The practical implication: quantum-safe cryptography requires both algorithm selection and secure implementation. Hardware security modules (HSMs), constant-time programming, and formal verification become more important, not less.
Why the Timeline Has Accelerated
Recent hardware and algorithmic advances have compressed estimated timelines for CRQCs significantly. The Global Risk Institute‘s 2024 survey of 47 quantum computing experts found that the probability of a CRQC by 2034 has risen to 34%—double the 2022 estimate of 17%.
Several developments drive this acceleration. Google‘s Willow chip demonstrated below-threshold error correction with 105 superconducting qubits in December 2024, validating that adding physical qubits can reduce error rates exponentially. More critically, algorithmic optimizations have reduced estimated physical qubit requirements for breaking RSA-2048 from approximately 20 million to under 1 million—a 95% reduction.
For organizations, this means planning horizons have shortened. The question is no longer whether CRQCs will arrive but whether migration can complete before they do.
The Regulatory Landscape: Mandates Taking Shape
Government action on quantum-safe cryptography has moved from guidance to requirement across multiple jurisdictions. The US government requires federal agencies to inventory cryptographic systems and begin transitioning. Canada has set binding deadlines: PQC migration plans by April 2026, critical systems prioritized by 2031, and full migration by 2035.
The EU‘s Digital Operational Resilience Act (DORA) includes crypto-agility provisions that effectively require financial institutions to prepare for quantum-safe transitions. The G7 Cyber Expert Group has reinforced that early discovery, inventory, and migration planning are essential to reducing systemic risk.
For regulated industries and government contractors, quantum-safe cryptography is becoming a compliance requirement, not a discretionary investment.
Technical Implementation: How Organizations Start
The first step in any quantum-safe migration is cryptographic inventory. Most organizations do not know where RSA and ECC are used across their infrastructure. Endpoints—PCs, laptops, servers—contain cryptography that is often overlooked in PQC planning. Yet these endpoints are where keys are generated, TLS sessions originate, and sensitive data is decrypted.
Practical implementation typically follows a hybrid approach: deploying both classical and quantum-safe algorithms together during transition. Major browsers, cryptographic libraries (OpenSSL, BoringSSL), and CDNs (AWS CloudFront) have already deployed hybrid PQC key exchange in TLS 1.3. This proves that quantum-safe cryptography works at internet scale without breaking existing systems.
Organizations should prioritize long-lived data and signed assets first—the data most exposed to harvest-now-decrypt-later attacks. Certificate authorities, code signing, and firmware updates follow.
The Crypto-Agility Imperative
Quantum-safe cryptography is not a one-time migration. It is the beginning of ongoing cryptographic change. Algorithms will be broken. New standards will emerge. NIST has already selected HQC as a backup to ML-KEM, anticipating that some algorithms may fall.
Crypto-agility—the ability to replace cryptographic algorithms without replacing entire systems—has become a core architectural requirement. Organizations should design systems that separate cryptographic primitives from application logic, maintain cryptographic inventory databases, and automate certificate and key rotation. Manual processes cannot scale across tens of thousands of endpoints.
The organizations that treat cryptography as a managed, replaceable component will adapt fastest. Those that hardcode algorithms into applications will face expensive, painful migrations.
Conclusion
Quantum-safe cryptography has moved from academic research to operational necessity. The standards are final. The regulatory mandates are taking effect. The hardware progress is accelerating. Organizations that treat this as a distant future problem misread both the threat landscape and the regulatory trajectory.
The path forward is clear but not trivial. Cryptographic inventory, hybrid deployment, crypto-agility, and vendor alignment form the core of any credible migration plan. Start with visibility. Prioritize long-lived data. Build the capability to change algorithms continuously, not as a one-time project.
The question is not whether your organization will migrate to quantum-safe cryptography. The question is whether you will do it proactively, on your own timeline, or reactively, under pressure from regulators or auditors. The choice determines cost, risk, and competitive position. Act now.
FAQs
When will quantum computers break current encryption?
Estimates vary, but expert consensus places a 34% probability of cryptographically relevant quantum computers by 2034, with timelines accelerating due to recent hardware and algorithmic breakthroughs.
Is AES-256 vulnerable to quantum attacks?
No. Grover‘s algorithm reduces AES-256’s effective security from 256 bits to 128 bits, which remains practically secure. Symmetric encryption is not the primary concern—public-key RSA and ECC are.
What is the difference between PQC and QKD?
PQC is mathematical cryptography that runs on existing hardware. QKD uses quantum physics for key distribution but requires specialized optical equipment. Most experts recommend PQC first, then QKD for high-security point-to-point links.