Introduction
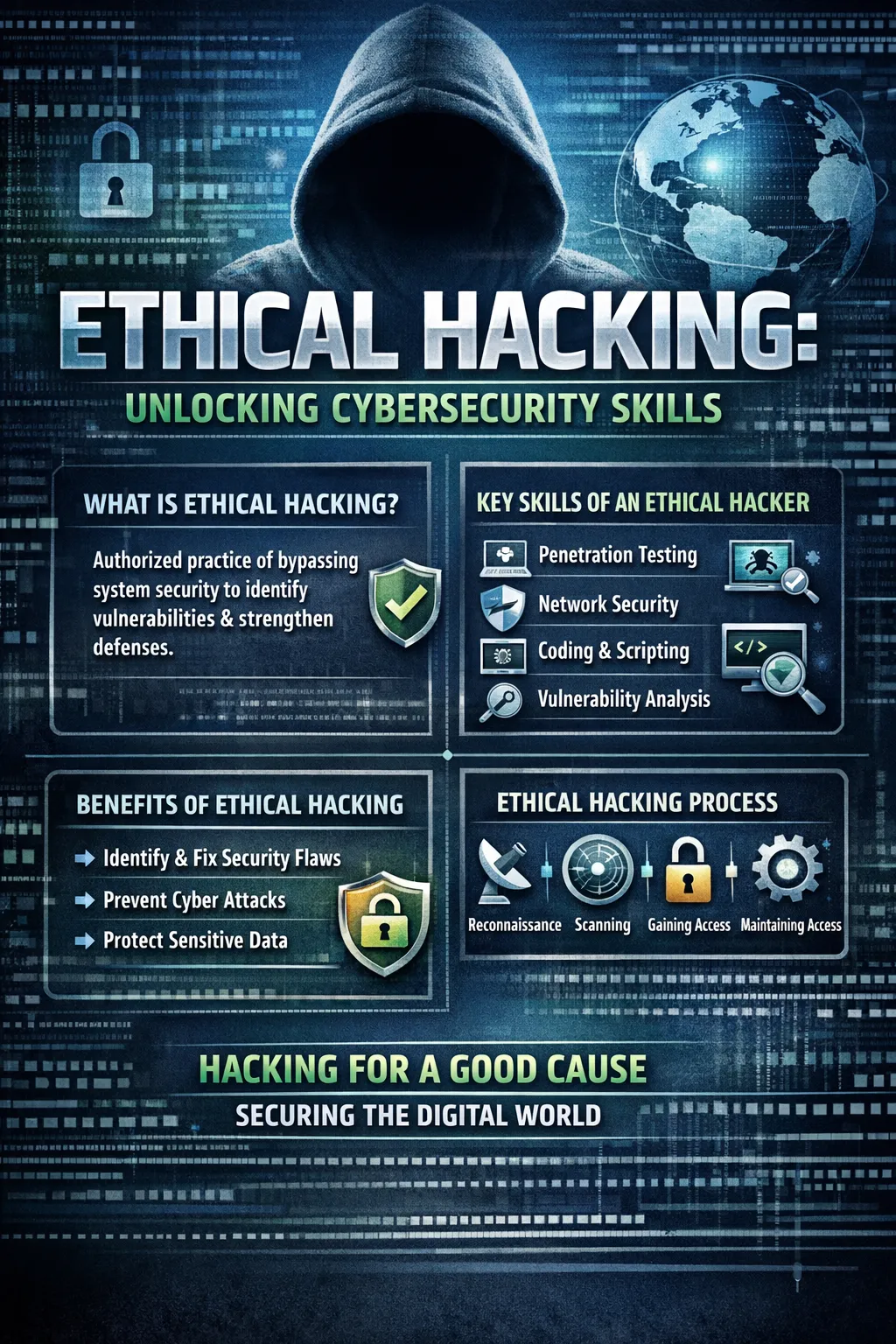
In an era where digital systems underpin every facet of modern life, the term “Ethical Hacking” often evokes confusion. At its core, Ethical Hacking is a sanctioned, defensive cybersecurity practice where experts employ the same tools and methodologies as malicious actors to proactively identify and remediate security weaknesses. This controlled, offensive approach is not a contradiction but a strategic necessity, transforming potential threats into a powerful mechanism for building resilient digital defenses. Understanding Ethical Hacking, its frameworks, and its critical distinctions is essential for any organization or professional committed to genuine security in an interconnected world.
Defining the Ethical Hacker’s Mandate and Code
An ethical hacker is a security professional retained by an organization to proactively uncover vulnerabilities before they can be exploited by adversaries with ill intent. Their work is governed by a strict, non-negotiable code of ethics that differentiates them from all other types of hackers. This code mandates explicit written permission from the system owner before any testing begins, a principle that establishes the legal foundation for all activities. Their actions must cause no harm to systems or data integrity, and all findings must be kept confidential and reported solely to the client. This structured, permission-based framework is what legitimizes the practice, ensuring it strengthens security without crossing legal or ethical boundaries.
The Hacker Spectrum: White Hats, Black Hats, and Grey Areas
The hacking community is broadly categorized by intent and legality, often visualized as a spectrum of hats.
- White Hat Hackers: These are the ethical hackers. They operate with full authorization, using their skills to improve organizational security, often through formal roles like penetration testers or security consultants.
- Black Hat Hackers: Motivated by personal gain, malice, or disruption, these individuals conduct unauthorized attacks to steal data, commit fraud, or sabotage operations. Their actions are purely criminal.
- Grey Hat Hackers: Occupying a legally ambiguous space, these hackers may exploit systems without permission but without malicious intent—often to expose a flaw and then notify the organization, sometimes requesting a fee or bounty. Despite potentially good intentions, their unauthorized access remains illegal and introduces significant risk.
Core Methodologies: The Ethical Hacking Lifecycle
Professional ethical hacking follows a systematic, multi-phase process to ensure thorough and controlled security assessments.
- Planning & Reconnaissance: The initial phase involves establishing the test scope and conducting footprinting to gather intelligence on the target using publicly accessible information and passive reconnaissance methods.
- Scanning & Enumeration: Using tools like Nmap, ethical hackers actively probe the network to identify live hosts, open ports, services, and detailed system information.
- Vulnerability Analysis & Gaining Access: Identified weaknesses are analyzed and then ethically exploited in a controlled manner to simulate a real breach and understand the potential impact.
- Maintaining Access & Post-Exploitation: This stage tests if an attacker could establish a persistent foothold in the system, mimicking advanced persistent threats to evaluate detection and response capabilities.
- Analysis & Reporting: The most critical phase for the client is compiling a detailed report of findings, exploited vulnerabilities, accessed data, and actionable remediation steps.
Essential Techniques and Tools of the Trade
Ethical hackers deploy a vast arsenal of techniques, each designed to test a different aspect of security.
- Penetration Testing: Simulating targeted attacks on networks, web applications, or physical security to exploit chained vulnerabilities.
- Social Engineering: Assessing the human layer by using phishing, pretexting, or baiting to test employee awareness and security policies.
- Vulnerability Assessment: Automated and manual scanning to systematically identify, classify, and prioritize security weaknesses in systems and software.
- Network & Password Attacks: Using scanning tools (e.g., Nmap, Wireshark) and cracking tools (e.g., John the Ripper, Hashcat) to test network perimeters and authentication strength.
Key platforms like Kali Linux provide a curated, optimized penetration testing environment pre-loaded with hundreds of these essential tools, streamlining the professional’s workflow.
The Indispensable Legal and Ethical Framework
Why is a signed contract before any testing non-negotiable? Without it, identical activities are considered illegal under laws like the UK’s Computer Misuse Act or the U.S. Computer Fraud and Abuse Act (CFAA). A formal agreement defines the rules of engagement: the specific systems to be tested, the techniques permitted, the testing timelines, and the handling of sensitive data. This scope ensures the assessment is effective, controlled, and legally defensible, protecting both the tester and the client organization.
Building a Career: Skills, Certifications, and Pathways
A career in ethical hacking requires a blend of deep technical knowledge and principled conduct.
- Core Skills: Proficiency in networking, systems administration, scripting languages (Python, Bash), and a thorough understanding of operating systems are fundamental.
- Key Certifications: Industry-recognized credentials validate skills and commitment to ethics. These include:
- CompTIA Security+: A foundational certification for core cybersecurity concepts.
- Certified Ethical Hacker (CEH): A widely recognized credential focusing on attack vectors, tools, and methodologies.
- Offensive Security Certified Professional (OSCP): A hands-on, performance-based certification renowned for its rigorous practical penetration testing exam.
- Career Pathway: Many professionals start in general IT or network support, move into roles like security analyst, and then specialize through certifications and practical experience in penetration testing or red teaming. The demand is high, with ethical hackers in the UK commanding average salaries ranging from £53,000 to £98,000, reflecting their critical role.
The Strategic Value to Modern Organizations
Engaging ethical hackers moves security from a theoretical model to an evidence-based practice. It provides an attacker’s-eye view of defenses, revealing critical flaws that internal teams might overlook due to familiarity or architectural assumptions. This proactive discovery allows organizations to prioritize remediation based on real exploit risk, directly informing security investments and strengthening compliance with standards like GDPR, PCI DSS, or ISO 27001. Ultimately, it transforms security from a cost center into a demonstrable enabler of business trust and operational resilience.
Emerging Frontiers and Future Trends
The field continuously evolves to address new technologies and adversary tactics. Current frontiers include:
- AI-Powered Security Testing: Using machine learning to automate discovery, predict attack paths, and generate sophisticated phishing simulations.
- Expanding Attack Surfaces: Specialized testing for cloud infrastructures, IoT devices, blockchain applications, and serverless architectures is now essential.
- Advanced Simulation: Red Teaming—long-term, goal-oriented adversary simulation—and Bug Bounty programs are becoming standard for mature security programs seeking depth and continuous assessment.
Final Recommendations for Practitioners and Organizations
For aspiring professionals, mastery begins with fundamentals. Build a home lab, pursue foundational certifications like Security+, and gain hands-on experience through controlled practice on platforms like Hack The Box. For organizations, the key is to integrate ethical hacking strategically. Start with a well-scoped penetration test or vulnerability assessment, use the findings to drive a targeted remediation cycle, and consider adopting continuous testing models like bug bounties as your program matures. Always ensure engagements are conducted by reputable, certified professionals or firms that adhere to recognized schemes like CREST or NCSC CHECK.
FAQs
What is the difference between an assessment vulnerability and a penetration test?
A vulnerability assessment identifies and lists potential weaknesses, while a penetration test actively exploits those weaknesses to demonstrate their real-world impact and business risk.
Can ethical hacking guarantee that a system is completely secure?
No. Ethical hacking provides a snapshot of security at a point in time against known tactics. It significantly reduces risk but cannot guarantee absolute security due to evolving threats and constant system changes.
Is learning ethical hacking legal for beginners?
Yes, provided it is done in your own isolated lab environment or on specially designed legal practice platforms. Attacking any system without explicit authorization is illegal, regardless of your skill level.