Author: Usman Aslam
Introduction The modern healthcare landscape is fundamentally defined by data. The transition from paper charts to pervasive digital systems has created an unprecedented explosion of clinical information. Big data …
Introduction The Internet of Things represents a fundamental shift in how we interact with the physical world. At its core, IoT applications are the networking of physical objects embedded with …
Introduction The Internet of Things Data has transformed the way devices communicate, collect, and share information. IoT Data refers to the information generated by connected devices, sensors, and systems …
Introduction How e-Bike Technology is transforming modern transportation by combining traditional cycling with electric-powered systems for efficient and eco-friendly travel. This innovative solution uses rechargeable batteries, electric motors, and …
Introduction In the age of artificial intelligence, the Cloud Data Center has grown far beyond its original role as a place to store data. Today, a Cloud Data Center functions as …
Introduction The global race to operationalize Electric Vertical Takeoff and Landing (eVTOL) aircraft is entering its most critical phase. After years of prototypes and promises, the eVTOL industry is …
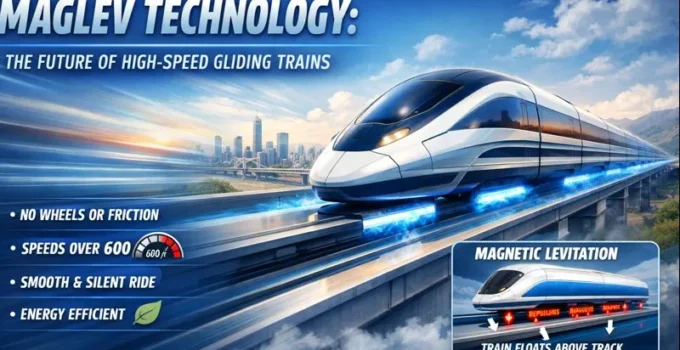
Introduction Magnetic levitation (maglev) represents the pinnacle of modern rail innovation, enabling trains to float above their guideways without physical contact. Driven by powerful electromagnetic forces instead of wheels …
Introduction Self-driving car (AV) technology, often called autonomous vehicle (AV) technology, refers to the sophisticated integration of sensors, artificial intelligence, and machine learning systems that enable a vehicle to navigate …
Introduction The concept of Supply Chain in blockchain has gained significant attention in recent years as businesses seek greater transparency, efficiency, and security in their operations. Understanding the Supply …
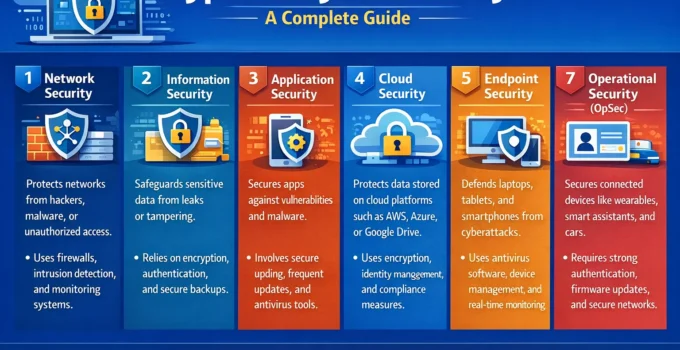
Introduction In today’s digital age, understanding the different Types of Cybersecurity is essential for protecting data, networks, and systems from ever-growing threats. In today’s digital landscape, understanding the distinct …