Introduction
Internet of Things in Cybersecurity represents the critical practice of protecting interconnected devices, their data, and the networks they operate on from evolving cyber threats. As projections estimate 31 billion connected devices by 2030, securing this vast and vulnerable attack surface has become non-negotiable. For years, IoT security has been the “awkward teenager” of technology—innovative but reckless, prioritizing connectivity over protection. However, a powerful convergence of regulatory mandates, standardized practices, and advanced technologies is forcing the ecosystem to mature.
This evolution is transforming the Internet of Things in Cybersecurity from a marketing afterthought into a foundational, accountable component of every connected device’s lifecycle. As digital ecosystems expand, strengthening the Internet of Things in Cybersecurity is essential to ensuring long-term resilience, trust, and secure innovation.
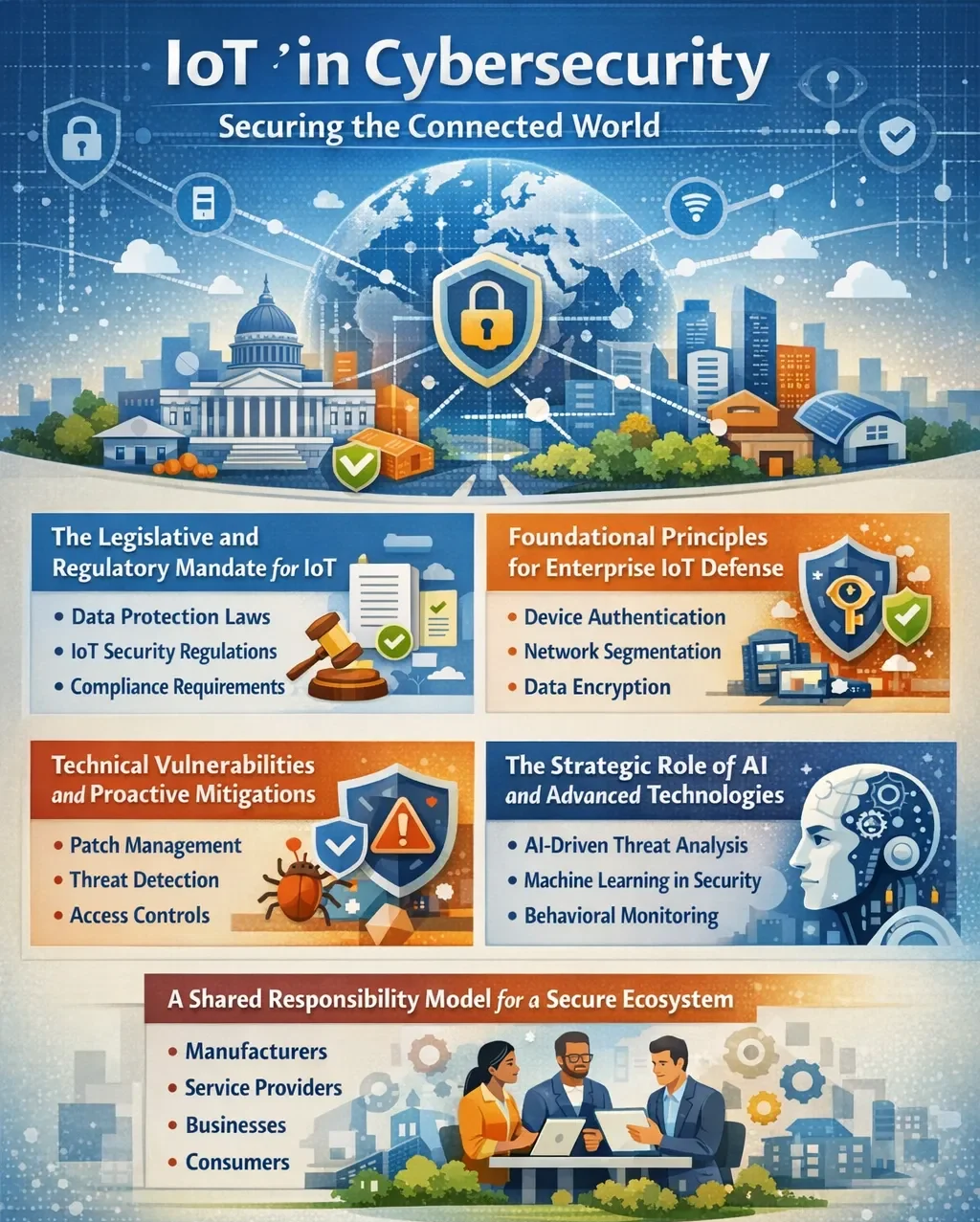
The Legislative and Regulatory Mandate for IoT
A transformative wave of regulation is compelling manufacturers and enterprises to prioritize IoT security. These laws are establishing clear accountability and enforceable baselines for the first time.
- The EU Cyber Resilience Act (CRA): This landmark legislation introduces mandatory “security-by-design” principles. Manufacturers of products with digital elements—including IoT devices—must report severe cybersecurity incidents and actively exploited vulnerabilities within strict 24 to 72-hour windows. By late 2027, full compliance with security requirements, including vulnerability handling and support periods, becomes mandatory.
- Expanded EU and UK Cybersecurity Frameworks: The NIS2 Directive, actively enforced across the EU, significantly broadens the scope of regulated entities, demanding robust risk management and incident reporting. In the UK, the upcoming Cyber Security and Resilience Bill expands obligations and introduces tougher penalties for non-compliance. The updated Cyber Essentials scheme (v3.3) also mandates Multi-Factor Authentication (MFA) for all cloud services, explicitly bringing all internet-connected IoT devices into scope.
- The U.S. Cyber Trust Mark: This voluntary but influential labeling program, championed by the FCC, creates a consumer-facing security standard. Products bearing the mark and its accompanying QR code must meet defined cybersecurity criteria, creating market incentives for manufacturers to build more secure devices.
Foundational Principles for Enterprise IoT Defense
Beyond compliance, effective IoT security is built on core technical principles that address its unique challenges of scale, heterogeneity, and resource constraints.
- Secure-by-Design Philosophy: Security must be embedded at the hardware level from the initial design phase, not bolted on post-production. This includes threat modeling, secure coding practices, and implementing hardware roots of trust.
- Robust Identity and Authentication: Each device must have a unique, cryptographically verifiable identity, often through digital certificates and Public Key Infrastructure (PKI). This is critical for preventing impersonation and enabling secure communication between devices and platforms.
- Data Protection through Encryption: Data must be encrypted both in transit and at rest to prevent interception and manipulation. Strong encryption and key management are non-negotiable, even with devices that have limited processing power.
- Network Segmentation and Least Privilege: IoT devices should operate on segmented networks, isolated from critical IT and operational technology (OT) systems. Applying the principle of least privilege ensures devices and users have only the minimum access necessary, containing potential breaches.
Technical Vulnerabilities and Proactive Mitigations
The IoT threat landscape is defined by persistent, exploitable weaknesses. Enterprise security strategies must directly target these common vulnerabilities.
| Vulnerability/Risk | Primary Impact & Consequence | Proactive Mitigation Strategy |
| Weak/Default Credentials | Unauthorized device access; initial foothold for lateral movement. | Mandate strong, unique passwords; implement MFA or certificate-based authentication; and automate detection of brute-force attempts. |
| Insecure Communication | Data interception & man-in-the-middle attacks; loss of integrity. | Enforce end-to-end encryption (e.g., TLS 1.3+); use secure protocols like MQTT with TLS; and ensure forward secrecy. |
| Outdated Firmware | Exploitation of known, unpatched vulnerabilities; device takeover. | Establish automated patch management, maintain a real-time device inventory, and test patches before broad deployment. |
| Insecure Network Services | Exposure of unnecessary attack surfaces (open ports, APIs). | Harden devices by disabling unused services; deploy IoT-aware firewalls; implement strict API security and gateway controls. |
| Poor Device Management | Lack of visibility; orphaned or unauthorized devices on the network. | Maintain a comprehensive, dynamic asset inventory, use automated network discovery tools, and enforce lifecycle management policies. |
The Strategic Role of AI and Advanced Technologies
As IoT networks grow, traditional manual defense becomes impossible. Advanced technologies are essential for scaling protection.
- AI for Anomaly Detection and Response: AI and machine learning excel at establishing behavioral baselines for vast numbers of devices. They can detect subtle, anomalous activities indicative of a compromise—such as a sensor transmitting data at unusual times or volumes—far faster than human analysts. This enables real-time threat detection and automated response at machine speed.
- The Dual-Edged Sword of AI: Offensively, AI will empower attackers to create more adaptive malware and generate deceptive data to poison IoT systems. Defensively, it necessitates “explainable AI” in security tools so that automated decisions can be understood and trusted by human security teams.
- Unified IT/OT/IoT Security Platforms: Siloed security is ineffective. Modern solutions provide unified visibility across information technology (IT), operational technology (OT), and IoT environments, allowing security teams to trace an attack from a compromised IoT sensor through to corporate networks.
A Shared Responsibility Model for a Secure Ecosystem
Ultimately, securing IoT is a chain of accountability where the weakest link defines overall risk. Responsibility is distributed across the ecosystem.
- Manufacturers are accountable for secure-by-design development, providing timely security patches, and transparently communicating support lifecycles.
- Organizations must maintain complete asset visibility, enforce network segmentation, deploy advanced monitoring, and integrate IoT into their broader incident response planning.
- End-users and operators bear responsibility for changing default credentials, applying updates promptly, and following secure configuration guidelines.
Conclusion
The trajectory for IoT in cybersecurity is set toward irreversible maturity. The confluence of stringent regulations like the CRA, market-driven standards like the U.S. Cyber Trust Mark, and the operational necessity of AI-driven defense is creating a new paradigm. The industry is shifting from chasing rapid deployment to respecting the profound complexity and consequence of the connected world it has built. The task now is to operationalize this maturity, embedding security as a continuous, foundational practice across every layer of the IoT ecosystem.
Frequently Asked Questions
What is the biggest IoT security risk?
While technical vulnerabilities persist, the most significant risk is the lack of clear accountability across the device lifecycle, which new regulations are now forcefully addressing.
Are consumer IoT devices a real threat to enterprises?
Yes. Insecure consumer-grade devices on corporate networks or in employees’ home offices can serve as entry points for attackers to pivot into enterprise systems, especially with widespread remote work.
How does IoT security differ from traditional IT security?
IoT security must account for extreme device heterogeneity, long lifecycles, severe resource constraints (power, processing), and direct interaction with the physical world, requiring specialized tools and strategies.