Introduction
The convergence of Artificial Intelligence and Cybersecurity is defining a new era of digital risk and resilience. No longer a speculative future trend, it is the present reality, characterized by a dual-use technology that simultaneously empowers defenders and equips attackers. In the UK and US, informed organizations are moving beyond mere adoption, strategically balancing aggressive AI investment with a parallel, often greater, emphasis on cyber resilience. By combining automation, predictive analysis, and intelligent monitoring, Artificial Intelligence and Cybersecurity work together to deliver faster detection, stronger defenses, and smarter responses to evolving threats.
Success hinges not on choosing one over the other but on mastering their interplay—integrating Artificial Intelligence and Cybersecurity into a cohesive, governed, and human-supervised strategy.
The Investment Landscape: Cybersecurity Takes Precedence
Recent data indicates a pivotal shift in corporate investment strategy. While enthusiasm for artificial intelligence remains high, with 84% of UK firms planning some level of increased investment, cybersecurity is now the top priority for major budget increases. This rebalancing reflects a pragmatic response to high-profile attacks and the realization that rapid AI adoption can create new defensive gaps. The strategic imperative is clear: AI-driven growth must be built on a foundation of cyber resilience from day one.
The Defensive Arsenal: AI as a Force Multiplier
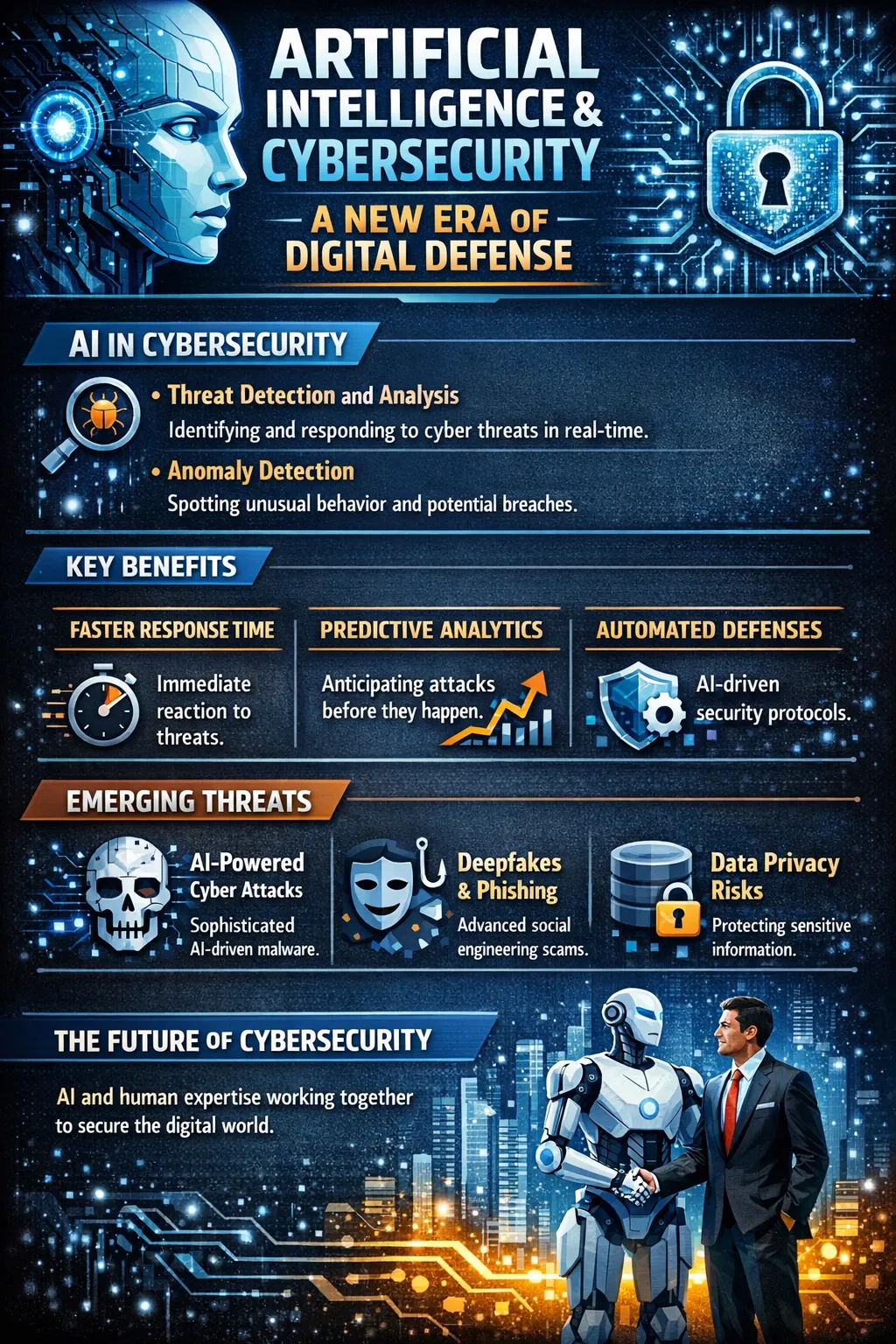
AI is revolutionizing security operations by automating complex tasks and enhancing predictive capabilities. Its primary value lies in speed, scale, and pattern recognition beyond human capacity.
- Proactive Threat Detection: AI systems analyze network traffic, user behavior, and endpoint activities in real-time to identify anomalies and subtle attack patterns that evade traditional signature-based tools. This shift from reactive to proactive defense is crucial against threats like ransomware.
- Automated Incident Response: Upon detecting a threat, AI can execute predefined containment actions—such as isolating infected systems or blocking malicious data transfers—within milliseconds, drastically reducing the window for damage.
- Enhanced Security Postures: AI enables the practical implementation of advanced frameworks. It can dynamically enforce zero-trust policies by continuously assessing access requests and can secure vulnerable IoT and cloud environments through behavioral monitoring and adaptive controls.
The Offensive Threat: AI-Powered Cybercrime
The democratization of AI is a double-edged sword, dramatically lowering the barrier to entry for cybercriminals. Attackers leverage the same technologies to create more potent, evasive, and scalable attacks.
- Hyper-Personalized Social Engineering: Generative AI crafts flawless, personalized phishing emails and creates convincing deepfake audio or video to impersonate executives, making fraudulent instructions highly believable.
- Evolving Malware & Evasion Techniques: Criminals use AI to develop adaptive malware that can alter its code to avoid detection and to launch “adversarial attacks” designed to fool AI-based security models by feeding them deceptive data.
- Automated Attack Scaling: AI tools allow a single actor to generate malware variants and automate attacks at an unprecedented scale and speed, challenging even well-resourced security teams.
Unique AI-Specific Security Vulnerabilities
Beyond supercharging traditional threats, AI systems introduce novel attack surfaces that require specialized understanding.
- Data Poisoning: Attackers corrupt the training data of an AI model, skewing its decisions and creating hidden backdoors. This compromises the model’s integrity at its core.
- Model Inversion & Theft: Proprietary AI models can be stolen via API abuse or reverse-engineered, leading to intellectual property loss. Furthermore, “model inversion” attacks can extract sensitive training data from a model’s outputs, risking data privacy.
- Supply Chain Complexity: AI development relies heavily on open-source frameworks and third-party code, each with dependencies that can number in the hundreds of thousands. Vulnerability in a single library can compromise the entire AI pipeline.
Foundational Best Practices for AI Security
Effective security in an AI-enabled environment requires a tailored, principle-based approach that extends traditional IT governance.
- Govern with an AI Bill of Materials (AI-BOM): Maintain a comprehensive inventory of all AI components—models, datasets, frameworks, and libraries—to manage risk and ensure visibility, especially against “shadow AI” used without official sanction.
- Implement Rigorous Model Vetting: Establish strict security requirements for any third-party or open-source AI model before integration, assessing data handling, access controls, and compliance certifications .
- Enforce Continuous Monitoring & Testing:AI models are non-deterministic; their behavior can drift. Implement continuous monitoring for anomalous outputs and integrate security testing (like adversarial simulation) into the CI/CD pipeline.
- Prioritize Human Oversight & Upskilling: AI augments but does not replace human expertise. Maintain human-in-the-loop review for critical decisions and invest in upskilling security teams to understand and manage AI-specific risks.
The Evolving Regulatory Horizon
The legal and compliance landscape is rapidly crystallizing, adding another layer of strategic consideration. In the UK, the Cyber Security and Resilience Bill aims to modernize regulations, expanding scope to managed service providers and introducing stricter incident reporting within 24 hours. Simultaneously, the EU AI Act is setting a global benchmark, categorizing AI systems by risk and imposing stringent requirements on high-risk applications. Organizations must navigate these parallel frameworks, often preparing for the most stringent standard to ensure compliance across jurisdictions.
Actionable Recommendations and Next Steps
- Conduct an AI Security Audit: Immediately inventory all AI tools in use—both sanctioned and “shadow AI”—and assess their data flows, access points, and compliance with internal policies.
- Adopt a Leading Framework: Structure your program around established guidelines. The MITRE ATLAS framework details adversarial tactics against AI, while the NIST AI Risk Management Framework provides a comprehensive governance structure.
- Fortify Your Third-Party Vetting: Scrutinize the AI security practices of every vendor. Update contracts to include explicit AI governance SLAs, data privacy guarantees, and breach notification protocols.
- Launch Cross-Functional Training: Bridge the knowledge gap between your security, data science, and legal teams. Ensure everyone understands the unique risks of AI, from data poisoning to regulatory liability.
Conclusion
The intersection of artificial intelligence and cybersecurity is not a temporary challenge but a permanent transformation of the digital battleground. The organizations that will thrive are those that reject a siloed view, recognizing that AI investment and cyber resilience are two sides of the same strategic coin. The path forward requires building security into the AI lifecycle from inception, governed by clear frameworks and continuous human expertise. As one industry leader succinctly put it, the winning formula is to “be brilliant at the basics” while strategically elevating your capabilities for this new era. The next step is to assess your organization’s posture against these evolving dual imperatives and begin building your integrated defense.
FAQs
Biggest AI cybersecurity threat today?
AI-driven social engineering, including deepfakes and advanced phishing, often exploits third-party vulnerabilities.
Affordable AI cybersecurity for small businesses?
Use managed security services, strengthen basic cyber hygiene, train staff against AI phishing, and assess cloud service security.
How do hackers use AI?
Cybercriminals use AI to create adaptive malware, advanced phishing, and evasion strategies.